Passwords serve as the first line of defense against data breaches, yet individuals often exhibit poor habits when it comes to selecting or updating their passwords regularly. Despite widespread requirements for secure passwords across applications and websites, research indicates that 75% of people globally disregard established best practices, with 64% opting for weak passwords or making only minor alterations when prompted to choose a new one rather than use a secure password generator.
Underestimating the security implications of choosing substandard passwords is a significant error, providing attackers with ample opportunities to infiltrate systems. Once assailants acquire valid password credentials, they can easily escalate their privileges to administrator or superuser levels, circumventing an organization’s identity management security measures.
Data breaches can severely tarnish a company’s reputation and result in substantial financial losses, meaning a concerted effort to enhance password practices and implement a robust identity security framework is needed. Consequently, forward-thinking organizations are adopting multi-factor authentication (MFA) to mitigate the risk of credential theft and unauthorized access. Through MFA, users gain access to applications and corporate networks by providing an additional form of verification, such as a code received via email or momentarily displayed on their phones.
Nevertheless, as companies embrace more secure authentication methods, attackers are devising innovative strategies to bypass MFA protections. These tactics include cookie theft, social engineering, and MFA fatigue-based attacks. So, while MFA offers greater security than traditional passwords, it is essential to recognize that attackers continuously seek ways to undermine it.
Companies must intensify their efforts to bolster identity security. Emerging threats present an opportunity to proactively address the escalating risk of data breaches, and while unconventional, a passwordless approach may offer a viable solution.
EMEA Technical Director, CyberArk.
Out with the old and in with the new
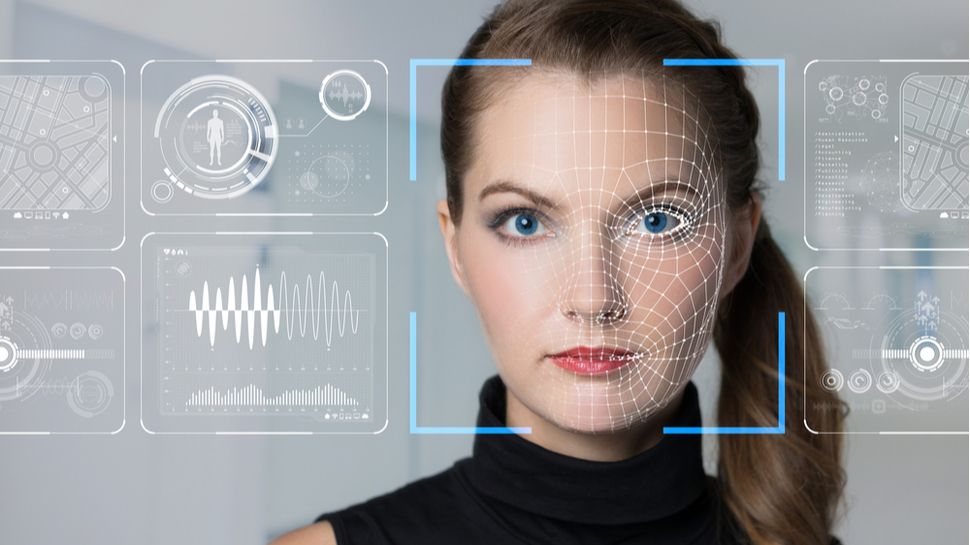
Businesses are slowly starting to give up traditional passwords to adopt passwordless approaches. With zero-password authentication, individuals can confirm their identity in various ways – whether it’s a QR code displayed at login or through biometric authentication like facial recognition – beyond a memorised password. This type of approach helps reduce risks of threat actors infiltrating networks, as private keys are unique and only accessible from the user’s local device. Overall, identity security is enhanced.
Additionally, it’s easier and more convenient for both users and IT teams to remove passwords. Users no longer need to remember their password or change it regularly, and IT no longer need to spend time assisting employees with account unlocks and password resets. This approach also has a positive impact on productivity thanks to a more seamless sign-in experience.
Making the transition to a passwordless system
It’s important to keep in mind that, while passwordless technology brings significant benefits, making this transition can’t be done overnight and some organizations might even never be able to adopt a completely passwordless approach. Removing passwords is a big commitment, particularly for businesses managing thousands of users, countless applications, hybrid and multi-cloud environments and complex login flows. There are just too many legacy systems deeply entrenched in IT infrastructure that require passwords.
So, it’s about finding the best approach for each company and what works from both an identity security and a cost point of view. The journey to zero-password authentication is unique to the requirements of every company, and the needs of every user. There is no one-size-fits-all approach. And with technology constantly evolving and user adoption increasing, successfully achieving an entirely passwordless environment involves a phased approach.
Consider all available solutions
While completely eliminating passwords may pose challenges for some businesses, they can still reduce their dependence on them by adopting appropriate identity and access management (IAM) solutions that facilitate passwordless functionalities. And when assessing IAM solutions, organizations should prioritize specific capabilities, such as:
1. Zero sign-on (ZSO) uses robust cryptographic standards such as certificates and mixes user identities with contextual information such as device fingerprints and security posture. It is the first pillar of a true credential-less solution. With ZSO, users can smoothly log in to their assigned applications and services once their devices have been checked and it’s confirmed they meet security posture requirements. Users don’t need any form of additional authentication. ZSO can be combined with other passwordless authentication factors best suited to the business requirements, enabling businesses to improve usability and increase identity security.
2. FIDO2 Web Authentication (WebAuthn) is widely supported by nearly every identity vendor and plays a pivotal role in enabling passwordless authentication for typical end users. Along with FIDO2, FIDO’s passkeys offer a new approach to achieving passwordless access across multiple devices, using users’ devices’ security capabilities to further enhance individuals’ experience. These passkeys are also highly resilient to phishing attempts, in other words, they can effectively mitigate attack vectors associated with MFA which necessitate human interaction.
3. With remote work now a prevailing trend, ensuring secure access for employees accessing a corporate network through a VPN is essential. In particular, using adaptive MFA is recommended as this adds an extra layer of identity security to remote access, protecting the company’s corporate network and on-site apps and resources, while ensuring a seamless login experience that continuously evaluates and adjusts as needed with passwordless factors based on contextual and risk analytics. Adaptive MFA as an approach is important and effective because it gives high-risk users or authorisation requests additional steps before access is granted and vice versa.
4. To achieve a true passwordless experience, it’s critical to deploy a solution that empowers users to self-enrol, replace and delete passwordless authenticators under appropriate security protocols, along with a wide variety of alternative passwordless authentication methods to choose from. For example, in the event of an individual losing their mobile phone, they should be able to replace the passwordless authenticator factor from various factors with the appropriate security controls.
Building defenses fit for the future
Businesses are increasingly adopting multi-factor authentication (MFA) to reduce the risk of threat actors stealing their passwords. But simply adding MFA as an extra layer on top of passwords is not quite a silver bullet. Instead, MFA should be incorporated as part of a passwordless experience, through push notifications, user context, etc. This creates a far more effective solution to preventing unauthorized access to corporate networks. Not only does this approach help improve identity security and organizational resilience against today’s cyber threats, but it also enhances user experience.
Nevertheless, transitioning to a passwordless system cannot occur instantaneously for any company. Such a shift demands strategic planning, disciplined execution, and heightened employee awareness. Robust leadership support is needed to ensure all staff members are adequately educated on the most effective practices for implementing passwordless authentication securely and efficiently. Moreover, forging partnerships with experienced and reputable vendors is crucial for the successful integration of passwordless systems within the organisation. To effectively anticipate and mitigate threats, companies must ensure that their IAM providers possess the requisite expertise to cater to their security requirements.
We’ve listed the best business password managers.
This article was produced as part of TechRadarPro’s Expert Insights channel where we feature the best and brightest minds in the technology industry today. The views expressed here are those of the author and are not necessarily those of TechRadarPro or Future plc. If you are interested in contributing find out more here: https://www.techradar.com/news/submit-your-story-to-techradar-pro